Every Salesforce architect eventually faces the same uncomfortable conversation: the org has accumulated years of shortcuts, and someone wants to know when to fix it. The honest answer is that zero debt is the wrong target, and pretending otherwise leads to worse decisions than the debt itself. There is no version of an enterprise Salesforce org with acceptable salesforce org technical debt acceptable levels at zero; the goal is classification, not elimination.
The problem is that most orgs treat technical debt as a binary. Either everything is clean, or the org is broken. Neither framing is useful. What actually matters is whether the debt you’re carrying is inert, degrading, or actively blocking your next architectural move.
Why “Zero Debt” Is the Wrong Target
Debt accumulates in Salesforce orgs for structural reasons, not just negligence. Business requirements arrive faster than architecture can absorb them. Declarative tools lower the barrier to building, which means more people build more things with less oversight. Org mergers, acquisitions, and platform expansions layer configurations on top of configurations.
In orgs coordinating across 15+ business units, the metadata sprawl is not a failure of governance; it’s a predictable consequence of scale. The architecture question is not how to eliminate that sprawl, but how to classify it.
The distinction that matters is between debt that is stable and debt that is compounding. A legacy validation rule that nobody touches, references a field that still exists, and fires on a record type that’s still in use is stable debt. It costs nothing to carry. A deprecated Flow that triggers on every Opportunity update, calls an External Services endpoint that now returns 404s, and silently fails without alerting anyone is compounding debt. Every day it runs, it erodes data quality and masks a real integration failure.
Treating both identically is a resource allocation failure. Ignore both, and compounding debt silently erodes data quality. Remediate both, and you waste cycles on inert configurations that were never going to fail.
A Risk-Tier Framework for Classifying Debt
The architecture that works here is a three-tier classification based on blast radius and trajectory, not age or complexity.
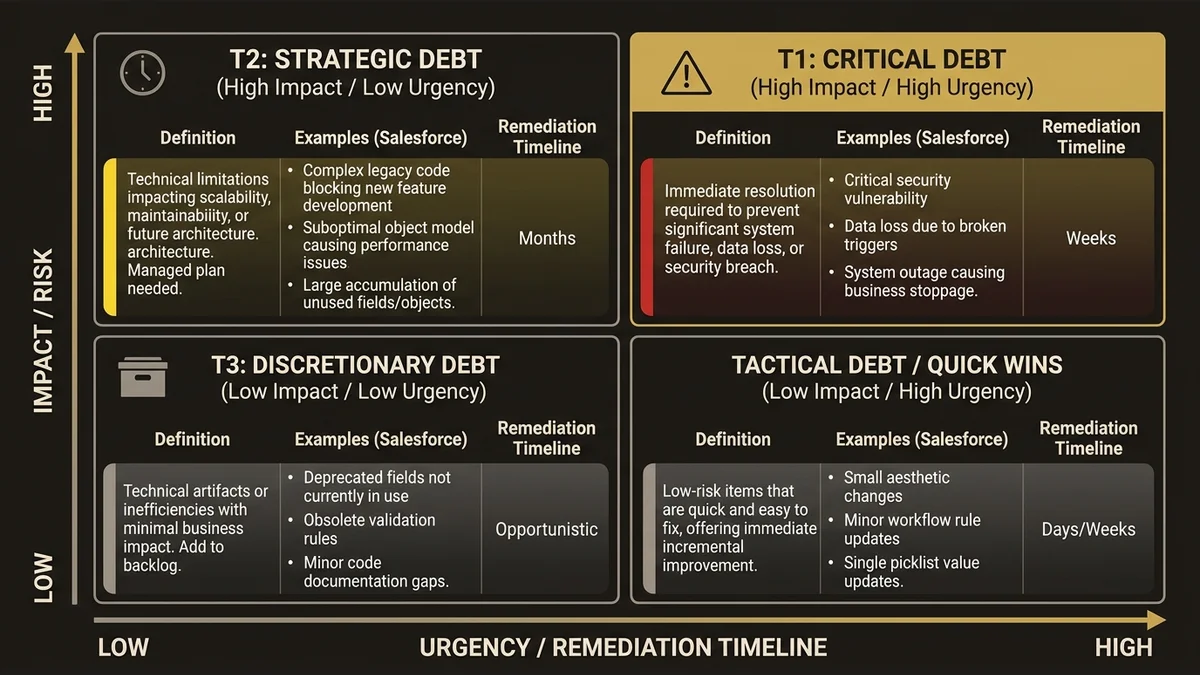
Tier 1: Active Risk. Debt that is currently degrading data quality, blocking platform upgrades, or creating compliance exposure. This includes Flows with unhandled fault paths that silently swallow errors, duplicate Identity Resolution configurations that produce conflicting Unified Individual records in Data Cloud, and custom code that bypasses sharing rules in ways that create GDPR or CCPA exposure. Tier 1 debt has a remediation deadline measured in weeks, not quarters.
Tier 2: Latent Risk. Debt that is stable today but will become Tier 1 under a foreseeable trigger. A common pattern is legacy Apex triggers written before bulk-safe patterns were standard; they work fine at current data volumes but will fail when a Data Cloud activation pushes a high-volume batch update through the CRM. Another example is hardcoded Record Type IDs in custom components that will break the moment someone runs a sandbox refresh. Tier 2 debt needs a remediation plan tied to the trigger event, not an open-ended backlog item.
Tier 3: Inert Debt. Configurations, fields, and code that are unused, undocumented, and untouched, but also harmless. Orphaned custom fields on Account with no field-level security exceptions, deprecated permission sets that are assigned to zero users, old report folders nobody accesses. This debt inflates metadata counts and slows deployments marginally, but it does not compound. The right posture is periodic cleanup during release windows, not emergency remediation.
The classification exercise itself is the deliverable. An org with 200 items of Tier 3 debt and zero Tier 1 items is in better shape than an org with 15 items total but three of them are Tier 1.
What Most Teams Get Wrong About Debt Assessment
The most common failure mode is running a static analysis tool, generating a list of “issues,” and treating the list as a remediation backlog. Tools like the Salesforce Optimizer or third-party metadata scanners are useful for discovery, but they produce output sorted by category, not by risk. A report showing 47 Flows without descriptions and 2 Flows with unhandled fault paths will list them in the same section. The 47 documentation gaps are Tier 3. The 2 fault path gaps might be Tier 1.
The second failure mode is conflating complexity with debt. A complex Flow orchestration that handles a genuinely complex business process is not debt; it’s appropriate architecture. Debt is complexity that exists because of a shortcut, not because of a requirement. A 400-line Apex class that does what a well-structured Flow could do is debt. A 400-line Apex class that handles a performance-sensitive bulk operation that Flow cannot execute efficiently is not.
This distinction matters because it determines whether you’re remediating debt or refactoring working architecture. Refactoring working architecture without a clear performance or maintainability gain is how teams introduce new bugs while claiming to reduce risk.
For a structured approach to running this kind of assessment, the Salesforce technical debt assessment framework covers the discovery and scoring methodology in detail.
When Acceptable Debt Becomes Unacceptable
The tier classification is not static. Debt migrates between tiers when the org’s context changes, and the most dangerous period is during platform expansion.
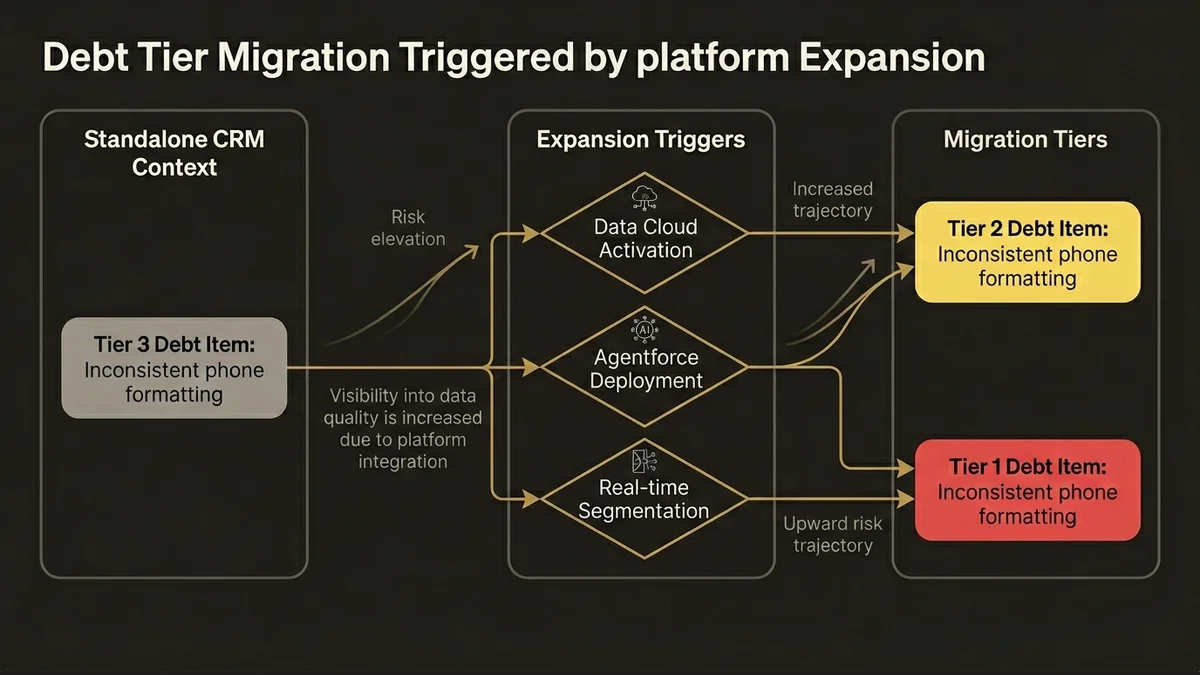
When an org adds Data Cloud, the risk profile of CRM-side data quality issues changes immediately. Identity Resolution rulesets depend on consistent field population; email format, phone normalization, account hierarchy integrity. Debt that was Tier 3 in a standalone CRM context (inconsistent phone field formatting across legacy records) becomes Tier 2 the moment you configure a Data Stream pointing at that field for identity matching. If you activate before cleaning it, you get fragmented Unified Individual records that are expensive to correct after the fact.
The same pattern applies to Agentforce deployments. The Atlas Reasoning Engine grounds its responses in the data it can access through configured Actions and Data Graphs. If the underlying CRM data has structural integrity issues; duplicate Accounts, orphaned Contacts, Opportunities in terminal stages that were never closed; the agent will surface those inconsistencies in its outputs. Hallucination in an LLM context is a model problem. Incoherent responses grounded in bad CRM data is an org health problem, and no amount of prompt engineering in Prompt Builder will fix it.
The forward-looking frame here is important: every major platform capability Salesforce is shipping in 2025 and 2026 assumes higher data quality than most orgs currently maintain. Agentforce, Data Cloud activation, and real-time segmentation all amplify existing data quality issues rather than abstracting over them. Debt that was tolerable in a workflow-automation context becomes a blocker in an AI-activation context.
This is the architectural argument for addressing Tier 2 debt proactively rather than waiting for the trigger event. By the time you’re mid-implementation on a Data Cloud or Agentforce project, remediating CRM-side data quality under time pressure is significantly more expensive than addressing it during a planned cleanup cycle. The Salesforce architecture review checklist provides a pre-expansion audit structure that surfaces these latent risks before they become active ones.
Building a Governance Model That Prevents Tier 1 Accumulation
Remediation is reactive. The architecture that prevents Tier 1 debt from accumulating in the first place is a governance model with teeth.
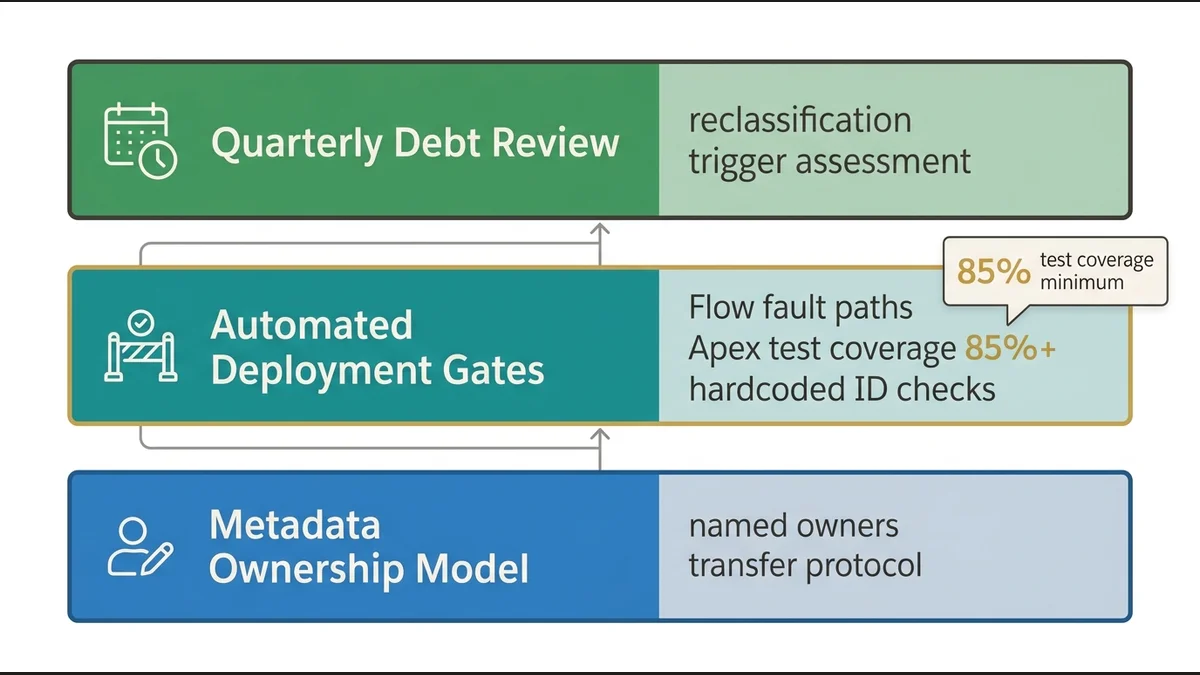
The governance floor for a mid-to-large org has three controls: a metadata ownership model, a deployment gate, and a quarterly debt review.
Metadata ownership means every Flow, Apex class, and integration configuration has a named owner responsible for its operational health. Not a team. A person. When that person leaves, ownership transfers explicitly. The honest caveat: in orgs with high admin turnover, named ownership decays within two cycles. The workaround is to tie ownership to a role definition (e.g., “Service Cloud automation owner”) attached to the active holder of that role, surfaced via a metadata-tagged custom object. It’s a heavier lift than a spreadsheet, but it survives turnover.
The deployment gate is a set of automated checks that run before any change reaches production. At minimum: Flow fault path coverage, Apex test coverage above 85% (not the platform minimum of 75%), and a check for hardcoded IDs.
The quarterly debt review is a structured session where the architecture team reclassifies existing debt items based on what changed in the org over the past quarter. New integrations, new Data Streams, new Agentforce Topics, each of these is a potential trigger that promotes latent debt to active risk. The review takes two to three hours and produces a revised tier classification with updated remediation priorities.
This is not a heavy process. It is a lightweight forcing function that prevents the “we’ll deal with it later” pattern from compounding indefinitely.
For orgs that have already accumulated significant Tier 1 debt and need a structured recovery path, the org health recovery services framework addresses prioritization and sequencing for distressed orgs.
Key Takeaways
- Classify, don’t eliminate. Zero debt is not the target.
- Tier 1 debt has a remediation deadline measured in weeks. Active data quality degradation, compliance exposure, silent failures.
- Debt migrates. Adding Data Cloud or Agentforce immediately elevates the risk profile of CRM-side data quality issues that were previously tolerable.
- Static analysis tools produce discovery output, not risk-ranked remediation backlogs. The classification work is manual and requires architectural judgment.
- Three governance controls (metadata ownership, deployment gate, quarterly review) prevent Tier 1 accumulation without a dedicated remediation team.
Need help with org health & recovery architecture?
Diagnose failing Salesforce implementations, eliminate technical debt, and architect recovery plans that get derailed projects back on track within 90 days.
Related Articles
Salesforce Centre Excellence : mise en place
Mettre en place un Centre d'Excellence Salesforce sans créer une bureaucratie paralysante. Architecture, gouvernance et jalons concrets pour les DSI.
Migration Salesforce zéro perte de données
Comment garantir une migration Salesforce zéro perte de données : architecture, pièges techniques et framework décisionnel pour DSI et architectes.
Gouvernance Salesforce : le framework qui tient
Sans salesforce gouvernance framework entreprise structuré, la dette technique s'accumule silencieusement. Voici l'architecture de gouvernance qui résis...