Agentforce IT Service adoption is accelerating faster than most enterprise architects anticipated. The question is no longer whether Salesforce can handle IT service management, but whether replacing your existing ITSM stack is architecturally sound or a trap dressed up as modernization.
The honest answer depends on what you’re actually running today, and most orgs are running something far messier than they admit.
Why Legacy ITSM Tools Create Architectural Debt
ServiceNow, Jira Service Management, and their predecessors were built around ticket queues and human routing logic. That model made sense when IT operations meant a help desk with a phone. It doesn’t map cleanly to an environment where infrastructure events, security alerts, employee requests, and vendor escalations all need contextual triage at machine speed.
The structural problem with legacy ITSM isn’t the UI or the licensing cost. It’s the data model. Most mature ITSM deployments have accumulated years of custom tables, workflow automations, and integration middleware that nobody fully understands. The configuration management database (CMDB) is typically 30-60% stale in orgs that haven’t run a dedicated hygiene program in the last 18 months. When you build AI-assisted routing or resolution on top of a stale CMDB, you’re not accelerating IT operations, you’re accelerating bad decisions.
Agentforce IT Service doesn’t solve the CMDB problem automatically. But it does force the question earlier in the architecture conversation, which is actually useful.
How Agentforce IT Service Actually Works at the Architecture Level
The Atlas Reasoning Engine is the core differentiator here. Unlike rule-based routing in traditional ITSM, Atlas reasons across multiple data sources simultaneously before taking action. In an IT service context, that means an incoming incident can be evaluated against the employee’s device profile, recent change records, known outage windows, and historical resolution patterns, all before a human sees the ticket.
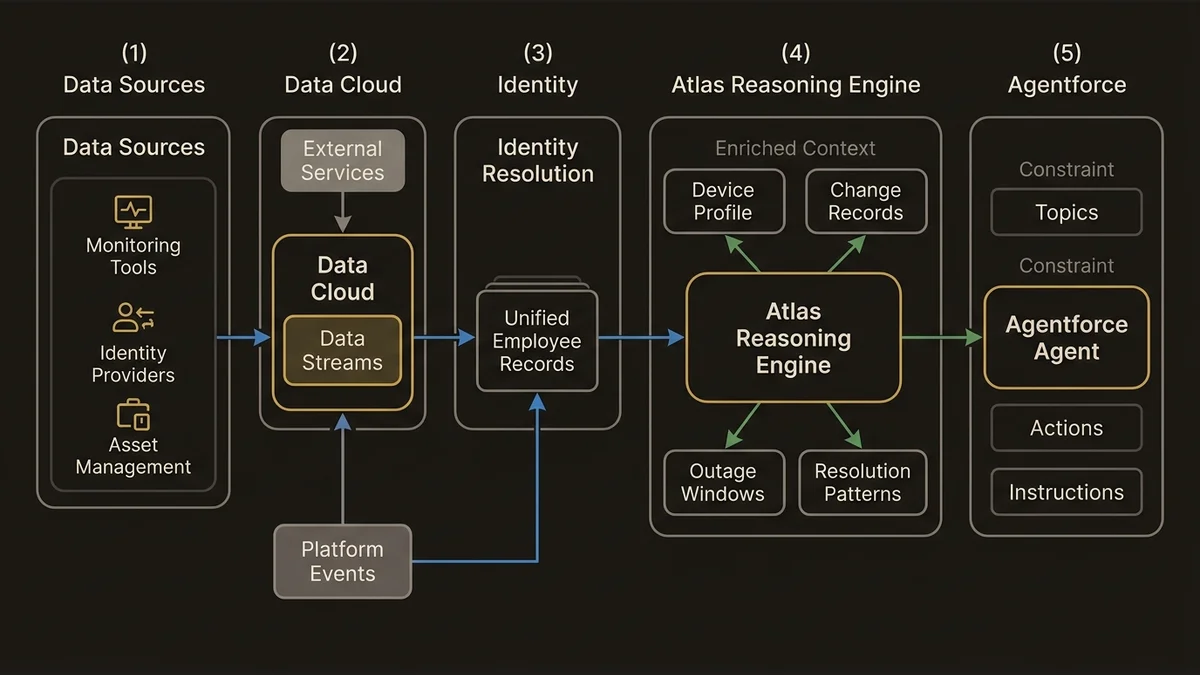
The practical architecture looks like this: Data Streams ingest from your monitoring tools, identity providers, and asset management systems into Data Cloud. Identity Resolution rulesets unify employee records across HR systems, Active Directory, and CRM. Calculated Insights surface things like “this employee has had three P2 incidents in 30 days, all related to VPN” as profile-level attributes. The Agentforce agent then reasons against that enriched context rather than a flat ticket form.
Topics and Actions define the agent’s operational scope. A well-designed IT service agent has tightly scoped Topics (password reset, software provisioning, incident triage, change approval routing) with explicit Instructions that constrain behavior. The failure mode in early Agentforce IT deployments is over-broad Topics that let the agent attempt actions outside its competency, which produces confident wrong answers. Scope discipline is not optional.
For integration with existing monitoring infrastructure, External Services handles REST-based connections to tools like PagerDuty, Datadog, or Dynatrace. Platform Events provide the real-time pub/sub layer for incident creation triggers. MuleSoft becomes necessary when you’re integrating with on-premise ITSM systems that don’t expose clean APIs, which is most of them.
Data Sovereignty Is the Underestimated Blocker
Enterprise IT operations data is some of the most sensitive data an organization holds. Incident records contain vulnerability disclosures. Change records expose infrastructure topology. Employee IT profiles reveal behavioral patterns that security teams treat as confidential.
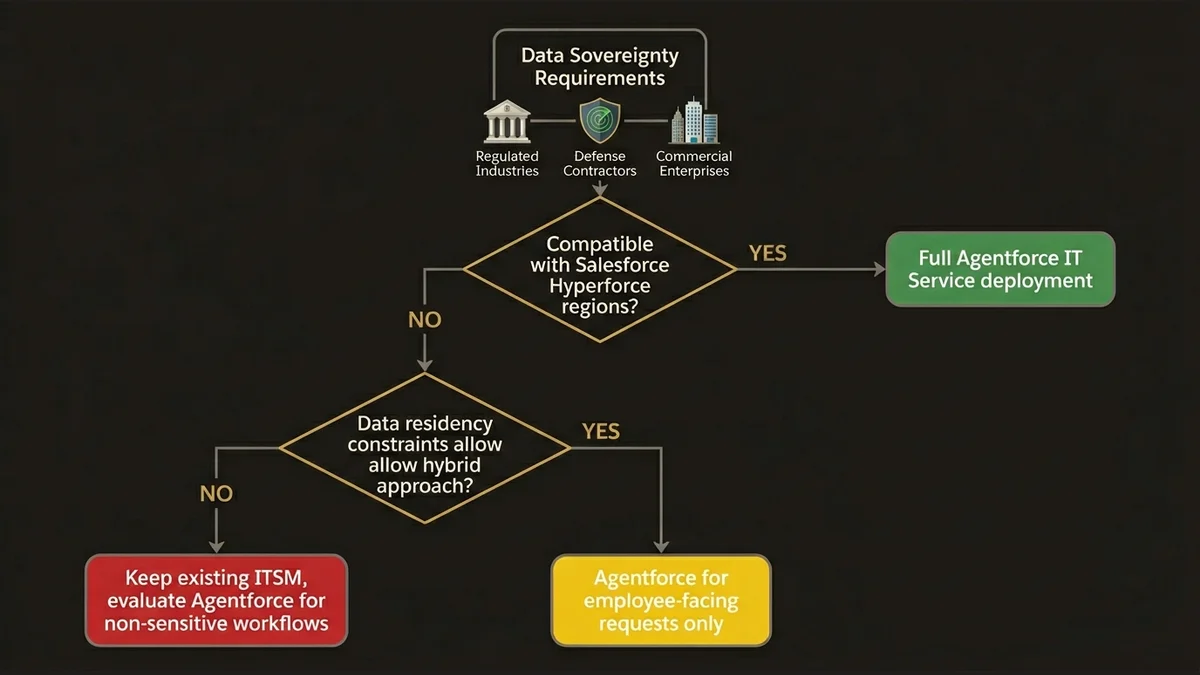
Running this through Agentforce means it transits Salesforce infrastructure. For most commercial enterprises, that’s acceptable under standard DPA terms. For regulated industries, defense contractors, or orgs with data residency requirements in jurisdictions where Salesforce’s hyperforce footprint doesn’t yet provide local processing guarantees, it’s a hard blocker.
The architecture decision tree here is binary: either your data sovereignty requirements are compatible with Salesforce’s current hyperforce region coverage, or they aren’t. There’s no middleware workaround that preserves the Atlas Reasoning Engine’s value while keeping sensitive data fully on-premise. Hybrid approaches where you strip PII before sending context to the agent work in theory but degrade reasoning quality significantly, because the agent loses the employee context that makes its responses useful.
Orgs in this position should evaluate Agentforce IT Service for the subset of IT operations that don’t touch sensitive infrastructure data, typically employee-facing service requests and tier-1 support, while keeping incident management and change control in their existing ITSM. That’s not a failure mode, it’s a realistic scoping decision.
The data governance architecture for Agentforce deployments in IT operations is covered in more depth in the Data Cloud implementation guide, which addresses how Data Streams and Identity Resolution interact with compliance constraints.
Scalability Patterns for Enterprise IT Operations
The scale question for Agentforce IT Service is different from the scale question for customer-facing Agentforce deployments. IT operations has lower volume but higher consequence per interaction. A customer service agent handling 10,000 sessions per day can tolerate a 2% error rate. An IT service agent that incorrectly provisions access or misroutes a P1 incident creates immediate operational risk.
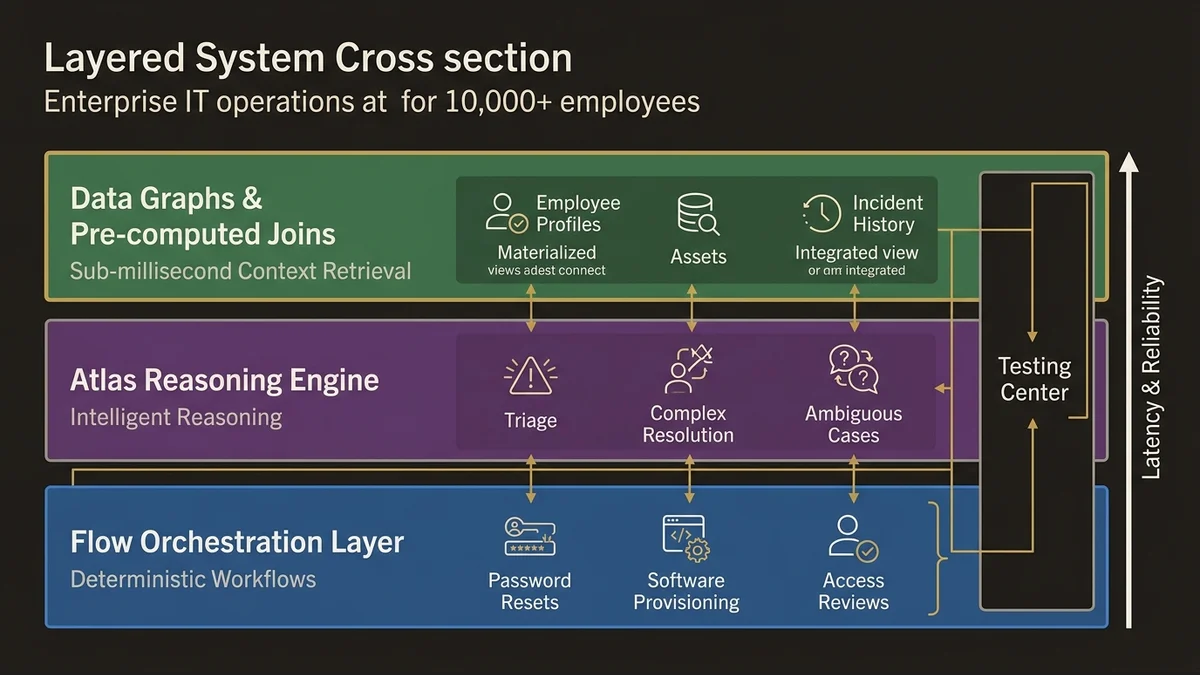
At enterprise scale, specifically orgs with 10,000+ employees and distributed IT operations across multiple regions, the architecture requires several deliberate choices.
First, Data Graphs become critical. Pre-computing joins between employee profiles, asset records, and incident history as materialized views means the agent retrieves context in milliseconds rather than running live queries across multiple DMOs at reasoning time. Without Data Graphs, latency compounds as incident volume grows, and the agent’s response time degrades precisely when IT operations is under the most stress.
Second, Flow orchestration handles the deterministic parts of IT service workflows. Not everything should go through Atlas reasoning. Password resets with verified identity, standard software provisioning from an approved catalog, and routine access reviews follow predictable paths that Flow handles more reliably and cheaply than LLM reasoning. The architecture that works here is a hybrid: Agentforce handles ambiguous triage and complex multi-step resolution, Flow handles the deterministic execution layer underneath.
Third, the Agentforce Testing Center is not optional for IT service deployments. The consequence of untested agent behavior in IT operations is higher than in most other domains. Regression testing against a library of historical incidents, including edge cases and adversarial inputs, should be part of the deployment pipeline before any production rollout. Orgs that skip this step because “it’s just internal IT” consistently discover failure modes in production that were entirely predictable.
For the broader architectural patterns around Agentforce agent design in enterprise contexts, the agent design patterns article covers Topics, Actions, and Instructions configuration in detail.
When Replacing Your ITSM Is the Wrong Move
Full ITSM replacement with Agentforce IT Service makes sense in a narrow set of conditions: you’re already deep in the Salesforce ecosystem, your ITSM tool is genuinely end-of-life or prohibitively expensive to maintain, and your data sovereignty requirements are compatible with Salesforce’s infrastructure.
It does not make sense if your existing ITSM has deep integrations with your CI/CD pipeline, security operations tooling, or infrastructure automation that would require rebuilding from scratch. The migration cost in those scenarios typically exceeds the value of the AI-assisted triage capability, at least on a 3-year horizon.
The pattern that actually delivers ROI in the near term is augmentation rather than replacement. Deploy Agentforce IT Service as the employee-facing intake layer, handling tier-1 requests and initial incident triage, while keeping your existing ITSM as the system of record for change management, CMDB, and complex incident workflows. The integration between the two runs through MuleSoft or External Services depending on your existing ITSM’s API maturity.
This approach lets you capture the productivity gains from AI-assisted triage without betting your IT operations on a platform migration that could take 18-24 months to stabilize. It also gives you time to address the CMDB hygiene problem before it becomes the Atlas Reasoning Engine’s problem.
The architectural evaluation for this kind of augmentation pattern overlaps significantly with the broader Agentforce implementation considerations covered in the Agentforce implementation guide. The IT service context adds the CMDB dependency and data sovereignty dimensions, but the core agent design principles apply directly.
For organizations ready to move beyond evaluation into architecture, the Agentforce architecture service addresses the full design scope including integration patterns, data model decisions, and governance frameworks for enterprise IT deployments.
Key Takeaways
- Agentforce IT Service adoption works architecturally when the Atlas Reasoning Engine has access to enriched employee and asset context via Data Cloud, not when it’s reasoning against flat ticket data.
- Data sovereignty is a binary constraint, not a configuration option. Regulated industries and orgs with strict data residency requirements need to scope Agentforce IT Service to non-sensitive workflows or wait for expanded hyperforce coverage.
- CMDB hygiene is a prerequisite, not a post-migration task. Stale asset and configuration data degrades Atlas reasoning quality before the agent handles a single incident.
- The hybrid architecture, Agentforce for intake and triage, existing ITSM for system of record, delivers faster ROI than full replacement and carries significantly lower operational risk on a 3-year horizon.
- Flow orchestration should handle deterministic IT service workflows. Routing every interaction through LLM reasoning is expensive, slower, and less reliable than reserving Atlas for genuinely ambiguous cases.
Need help with ai & agentforce architecture?
Design and implement Salesforce Agentforce agents, Prompt Builder templates, and AI-powered automation across Sales, Service, and Experience Cloud.
Related Articles

Agentforce Operations: Architecture Guide
Agentforce Operations redefines back-office automation. Here's the architectural blueprint for deterministic agent control planes at enterprise scale.
Salesforce Prompt Builder : bonnes pratiques
Prompt Builder mal configuré = agents Agentforce imprévisibles. Les bonnes pratiques architecturales pour éviter les pièges les plus coûteux.

Salesforce AI Specialist Cert Prep 2026
The Salesforce AI Specialist certification in 2026 tests architecture judgment, not recall. Here's how to prepare for what the exam actually measures.
